This provides a way for using different versions of a program based on the current directory name. By adding this example code to the .bashrc file, users can run a unique terraform version based on the directory name.
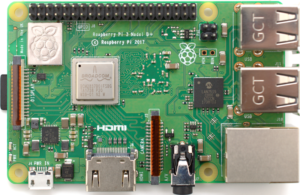
The Raspberry Pi 5 is critiqued for its high price and limited HEVC GPU video decoding. The Raspberry Pi 3B+ is recommended for small projects, while a Beelink Mini S12 Pro is suggested as an alternative that offers more power and comparable price without being on pre-order. For those wary of expenditure, a cheap laptop is also a viable option.
Red Hat Enterprise Linux 9 (RHEL 9) and Docker don’t get along very well. Running a container that requires older iptables (and not nftables) can be a problem.
I asked the OpenAI ChatGPT thing:
write a short story about chatgpt taking over the world
And here is what it came up with..
How to add an inline comment using Ansible.

I love Firefox. I’m a Firefox user, and hopefully always will be. Firefox is better than any other browser (plus it’s free and open-source). However, there have been a few technical things that I don’t like.
You can summarize Android 12 as “Extra Dim”, also known as: I upgraded to Android 12 and all I got was this lousy, bright gray dark theme.
The year is 2021, and I need to write a Windows Batch Script to get Helm Post-Renderer working on Windows so I can deploy my application to Kubernetes.
Like many people, I (have to) use Slack to collaborate with team members at work.
These are hard lessons I’ve learned so far.

Out of the box, security with Docker (and Docker Swarm) over the network is bad. Okay, that’s not entirely true. Out of the box when you have no containers started, it’s fine. But after you start a container, and if you publish a port, they are exposed to the outside world by default. And it’s not easy to fix. You need to create a custom Docker firewall with iptables.