
I love Firefox. I’m a Firefox user, and hopefully always will be. Firefox is better than any other browser (plus it’s free and open-source). However, there have been a few technical things that I don’t like.

I love Firefox. I’m a Firefox user, and hopefully always will be. Firefox is better than any other browser (plus it’s free and open-source). However, there have been a few technical things that I don’t like.

Out of the box, security with Docker (and Docker Swarm) over the network is bad. Okay, that’s not entirely true. Out of the box when you have no containers started, it’s fine. But after you start a container, and if you publish a port, they are exposed to the outside world by default. And it’s not easy to fix. You need to create a custom Docker firewall with iptables.
When testing Docker and iptables I stumbled upon something interesting. It appears Docker uses the iptables INPUT chain in an undocumented way. Well that’s interesting..
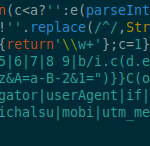
TL;DR: Website owners: Be careful when using third-party code that you don’t control.
Users: Hope for the best! Use a content blocker browser add-on like uBlock Origin. On your mobile device use Firefox with uBlock Origin.
Ansible is a great tool to automate all the things. Another task it can help to automate is user management. This guide will be talking specifically about user management on Linux servers like Red Hat Enterprise Linux (RHEL), CentOS, or Ubuntu. Ansible can handle this task!
Ansible can use encrypted files, using a feature called Ansible Vault. This is great for sensitive information that you don’t want to store as a normal text file since you are able to encrypt this data in your souce control.
SSH keys are convenient and more secure than using a password to authenticate. If you created your SSH key a while ago, it’s probably time to generate new RSA 4096 and Ed25519 keys. SSH keys like DSA and RSA 1024 are very old and now insecure. You should even upgrade ssh keys that are RSA 2048.
